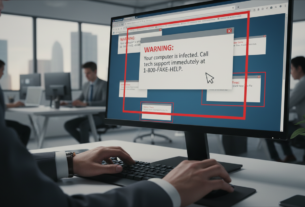
Did you know that cybersecurity teams ignore nearly one-third of all security warnings they receive? This startling statistic reveals a critical problem facing organizations today.
Security professionals face thousands of notifications daily. This overwhelming volume creates a condition known as alert fatigue. When teams receive too many warnings, their ability to respond effectively diminishes.
Alert fatigue affects operations across all company sizes. It stems from unmanaged notifications and poor prioritization systems. The constant stream of warnings desensitizes teams to genuine threats.
This comprehensive guide will help you navigate the complex world of cybersecurity notifications. You’ll learn to distinguish critical warnings from background noise. We’ll cover root causes, real-world impacts, and practical solutions.
The human element remains crucial in digital protection. Alert fatigue impacts not just operational efficiency but also team well-being and job satisfaction.
Key Takeaways
- Cybersecurity teams ignore approximately 30% of all security warnings due to overload
- Alert fatigue occurs when professionals receive too many notifications to process effectively
- This problem affects organizations of all sizes across every industry
- Failure to prioritize warnings creates vulnerabilities that attackers can exploit
- Distinguishing critical alerts from noise is essential for effective threat response
- Proper alert management protects both operational security and team mental health
- This guide provides strategies for identifying which warnings demand immediate attention
The Landscape of Security Alerts and Alert Fatigue
Security Operations Centers worldwide face an overwhelming tide of notifications that cripples their effectiveness. Teams receive approximately 17,000 malware warnings weekly, with only 19% considered reliable.
Real-World Examples of Alert Overload
This notification fatigue creates dangerous blind spots across industries. Healthcare facilities see critical cryptominer warnings buried under thousands of low-priority EDR alerts.
Manufacturing plants experience IDS notifications that mask malware attacks damaging robotic equipment. SaaS vendors face routine deployment alerts hiding vulnerabilities that expose customer information.
Financial institutions deal with noisy warnings that allow phishing scams to siphon client funds undetected.
Impact on Cybersecurity Operations
The 2025 Unit 42 Global Incident Response Report reveals shocking consequences. 13% of social engineering breaches occurred because warnings were ignored or left untriaged.
These incidents led to 60% data exposure rates compared to 44% across all attack types. Attackers deliberately exploit this fatigue using subtle tactics like SEO poisoning and malvertising.
The average data breach costs companies $3.86 million and takes 277 days to contain. Detection delays remain the biggest contributor to these staggering costs.
Root Causes of Security Alert Fatigue
The foundation of alert fatigue begins with the very tools designed to protect organizations. Modern enterprises deploy numerous solutions including SIEM, EDR, and cloud platforms. Each generates its own stream of notifications.
These overlapping systems create redundant warnings. Teams face an unmanageable volume of data. Complex IT environments with cloud applications and remote workforces multiply this problem.
Proliferation of Security Tools and Data Overload
Multiple protection systems working simultaneously create notification floods. Analysts receive alerts from different tools monitoring the same network activity. This duplication wastes valuable investigation time.
The increasing complexity of digital infrastructure contributes significantly. More devices and connections mean more potential triggers for warnings. This exponential growth overwhelms operational capacity.
Excessive False Positives and Staffing Challenges
Poorly tuned detection rules generate numerous false positives. Generic signatures often flag benign activities as threats. This creates noise that masks real dangers.
Analysts spend hours triaging non-actionable alerts. Meanwhile, genuine threats may go unnoticed. The cybersecurity talent gap compounds this issue.
Understaffed teams face ever-growing alert queues. Fewer analysts must process more notifications. This creates unsustainable workload pressure.
Key problems include:
- Overlapping tools generating duplicate warnings
- Insufficient context for effective prioritization
- High false positive rates from poorly configured systems
- Staffing shortages increasing individual workloads
Mitigating Security Alert Fatigue with Effective Triage and Automation
Effective notification management starts with rethinking how organizations generate and process their digital warnings. Strategic approaches transform chaotic streams into manageable workflows.
This requires continuous refinement of detection systems and intelligent automation. The goal is meaningful information rather than overwhelming volume.
Optimizing Alert Generation and Thresholds
Refining detection rule sensitivity reduces unnecessary notifications. Teams must understand normal network behavior patterns.
Adjusting thresholds minimizes warnings for common activities. This maintains protection while cutting noise significantly.
Automated Triage and Contextualization
Automated playbooks handle routine, low-risk notifications efficiently. They provide data enrichment and initial investigation steps.
Context integration transforms raw warnings into actionable intelligence. Asset importance and user roles guide prioritization decisions.
Centralized Alert Management Systems
Consolidating notifications into unified platforms simplifies oversight. SIEM and SOAR systems provide comprehensive visibility.
Key strategies include:
- Deduplication to eliminate redundant warnings
- Behavioral analytics for fewer false positives
- Unified dashboards for correlation and response
Understanding Security Alerts Calmly Through Context and Prioritization
Prioritization frameworks turn overwhelming digital warnings into clear action plans for cybersecurity teams. This methodical approach replaces reactive responses with structured incident handling.
Risk-Based Prioritization of Incidents
Each notification receives a risk score based on threat severity and asset criticality. This scoring system helps analysts focus on high-impact incidents first.
Establishing clear thresholds creates an efficient framework. Level 1 incidents demand immediate attention for critical threats. Level 2 requires action within set timeframes.
Level 3 issues can be addressed during normal operations. This systematic triage process ensures proper resource allocation.
Actionable Alert Management Strategies
Contextual information transforms vague warnings into actionable intelligence. Correlation of related notifications provides complete incident pictures.
Clear runbooks and standard procedures guide analysts through different alert types. This reduces ambiguity and improves response consistency.
Even junior team members can handle notifications effectively with proper guidance. Methodical approaches significantly outperform stress-driven reactions.
Leveraging Technology: SOAR, AI, and Behavioral Analytics
The integration of artificial intelligence and automation represents a paradigm shift in security alert management strategies. These advanced tools help teams process massive data volumes while identifying genuine risks.
SOAR Platforms and Automation Tools
Security Orchestration, Automation, and Response (SOAR) platforms handle repetitive tasks efficiently. They automate data enrichment and initial response actions.
This automation frees analysts to focus on complex threat investigations. SOAR systems significantly reduce manual workload in the soc environment.
AI-Driven Threat Analysis and Behavioral Insights
AI algorithms analyze vast security datasets to identify genuine threats. Machine learning continuously improves detection accuracy by learning from historical data.
Behavioral analytics establishes normal activity baselines. It then flags anomalous patterns that may indicate sophisticated attacks.
These technologies enable a shift from reactive response to proactive threat hunting. Teams can uncover hidden risks before they trigger automated warnings.
| Technology Type | Primary Function | Key Benefit | Implementation Impact |
|---|---|---|---|
| SOAR Platforms | Automate repetitive tasks | Reduces analyst workload | Faster initial response |
| AI/Machine Learning | Pattern recognition | Fewer false positives | More accurate threat detection |
| Behavioral Analytics | Anomaly detection | Identifies novel attacks | Proactive threat hunting |
| Threat Intelligence Integration | Context enrichment | Better prioritization | Informed decision-making |
Agentic AI solutions can autonomously handle initial alert analysis. They provide real-time insights that augment human analysts’ capabilities.
Optimizing Team Processes and Reducing Burnout
The human toll of continuous alert monitoring extends far beyond operational metrics, directly impacting analyst well-being and retention. A Promon survey revealed a critical issue: two-thirds of professionals experienced burnout in 2022, with over 50% citing workload as the primary cause.
This constant pressure leads to high turnover among skilled staff. Losing experienced talent makes remaining teams more vulnerable and increases recruitment costs.
Regular Review, Training, and Feedback Loops
Establishing routine processes is vital for sustainable operations. Regular reviews of detection rules and response playbooks, informed by frontline analyst feedback, help refine the system over time.
Cross-training initiatives are equally important. They allow team members to broaden their skill sets across different domains.
- Improves operational flexibility and resilience.
- Enhances job satisfaction by providing variety.
- Creates a more versatile security teams structure.
Enhancing Team Well-Being and Skill Development
Directly addressing burnout requires proactive initiatives. Effective strategies include clear workload management and access to mental health support resources.
Structured professional development opportunities also play a key role. Investing in your teams not only reduces fatigue and turnover but also improves the overall quality of threat response.
Long-Term Best Practices for Sustainable Security Operations
Organizations that thrive in today’s dynamic threat environment prioritize iterative enhancement of their protective measures. Sustainable success requires embedding continuous improvement into daily workflows.
Continuous Improvement and Adaptation
Regular reviews of detection rules and response playbooks keep systems optimized. Establishing feedback loops between analysts and engineering teams ensures frontline experience shapes future adaptations.
This approach transforms reactive operations into proactive protection cultures. Teams focus on threat hunting and vulnerability management before issues escalate.
Integrating Threat Intelligence and Incident Response
Effective integration provides critical context about emerging risks and attacker methods. This intelligence guides prioritization decisions during incident handling.
Knowledge sharing builds collective expertise across protection teams. Documented practices strengthen overall defensive postures through collaborative learning.
| KPI Category | Measurement Metric | Target Range | Review Frequency |
|---|---|---|---|
| Efficiency | False Positive Rate | <15% | Monthly |
| Response Time | Mean Time to Respond (MTTR) | <30 minutes | Weekly |
| Workload | Alerts Requiring Manual Triage | <100 daily | Quarterly |
| Team Health | Analyst Satisfaction Scores | >85% | Bi-annual |
Demonstrating ROI for automation investments justifies continued organizational support. These metrics guide strategic decisions for sustainable operations.
Conclusion
Sustainable incident handling requires balancing advanced tools with human expertise and well-being initiatives. The business impact of notification overload is severe, with breaches costing millions and detection taking months.
A multi-faceted approach combining technology, process optimization, and team support creates effective protection. Modern platforms now provide unified incident narratives instead of chaotic warning streams.
This evolution transforms teams from reactive responders to strategic defenders. They can focus on proactive threat hunting before attacks succeed.
Continuous improvement through regular reviews and adaptation ensures long-term success. Methodical approaches based on context and prioritization protect data while supporting business objectives.