Did you know that deceptive online schemes account for more than one-third of all security incidents? This startling fact highlights a major threat in our connected world.
Criminals use clever tricks to appear as trusted helpers. They create a false sense of urgency to trick people. The goal is to steal sensitive details like passwords or financial data.
These deceptive attempts have moved far beyond basic email scams. They now appear as text alerts, social media direct messages, and even pop-ups in video games. This makes awareness across all digital platforms essential.
While technology filters catch many threats, sophisticated ones often slip through. This makes your own knowledge the most powerful shield. Learning the warning signs protects you from significant harm.
Key Takeaways
- Deceptive online messages are a leading cause of security problems today.
- Attackers use psychological pressure, like urgency and fear, to manipulate victims.
- These scams are not limited to email; they appear on many digital platforms.
- Human vigilance is the last and most critical line of defense.
- Recognizing the signs of a fraudulent message can prevent financial and data loss.
Understanding the Phishing Landscape
Understanding the full scope of digital deception requires tracing its evolution from basic email fraud to today’s complex threat ecosystem. The term “phishing” emerged in the 1990s, blending “phreaking” (early phone hacking) with “fishing” for victims.
This social engineering approach involves criminals posing as trusted sources. Their goal is to trick people into revealing sensitive data through convincing communication.
Defining Phishing and Its Variants
Phishing represents a broad category of cyber attacks. Criminals send mass messages designed to look official. They hope a small percentage of recipients will respond.
Several dangerous variants have developed over time. Spearphishing targets specific individuals with personalized content. Smishing uses SMS texts to reach mobile users.
Vishing involves fraudulent phone calls from spoofed numbers. Each variant employs different channels but shares the same malicious intent.
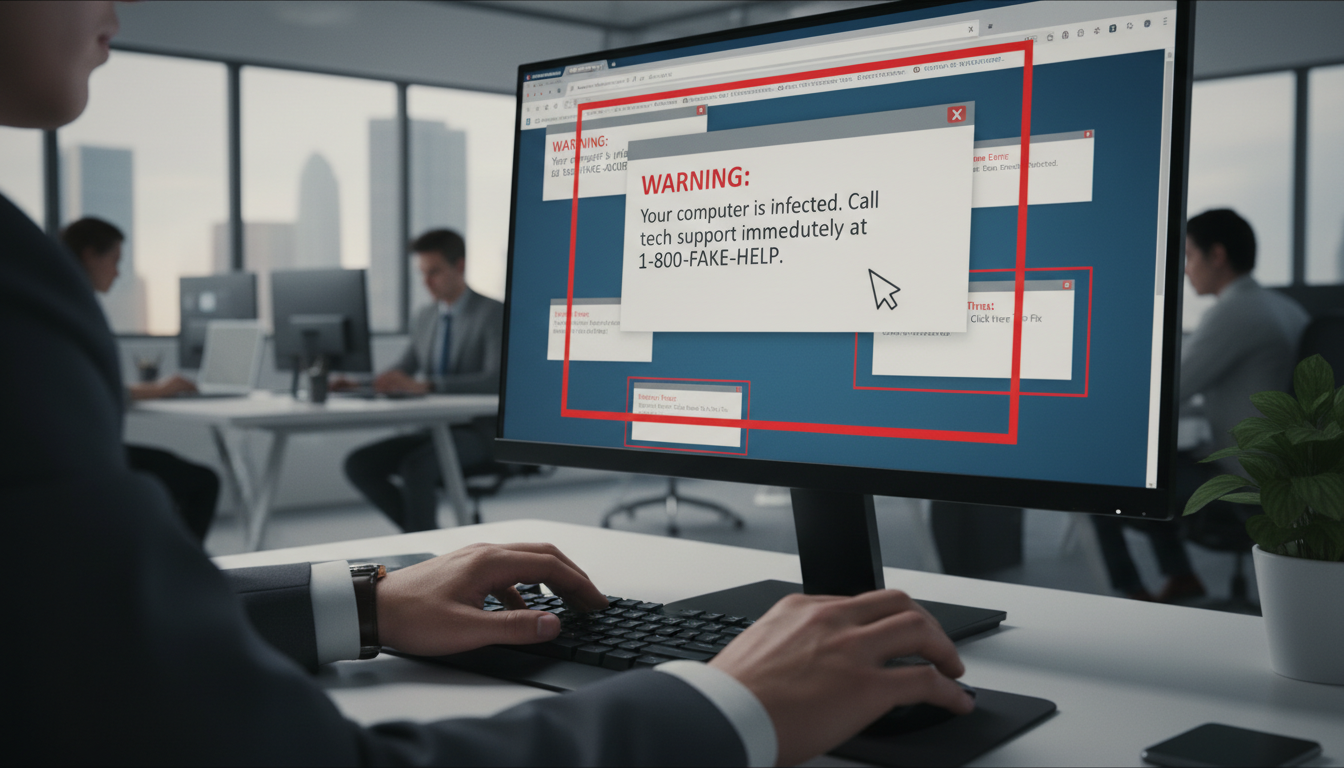
How Fake Support Messages Fit into the Cyber Threat Spectrum
Impersonating IT help desks or customer service represents a specific phishing tactic. Attackers exploit the trust people place in these support roles.
These deceptive communications fit within the broader phishing framework. They use similar psychological tactics as other variants. The objective remains stealing credentials or installing malware.
Regardless of the method, all these attacks aim for unauthorized access. Recognizing their common patterns is crucial for protection.
Recognizing Common Red Flags in Suspicious Messages
Several clear indicators separate authentic support communications from malicious attempts to steal information. Learning these warning signs can prevent significant data loss from sophisticated scam attacks.
Urgent Calls to Action and Generic Greetings
Artificial urgency represents the number one red flag in fraudulent messages. Criminals pressure victims to act immediately without thinking. They create false scenarios requiring instant response.
Common tactics include account suspension warnings and limited-time offers. Generic greetings like “Dear Customer” also signal danger. Legitimate companies use your actual name in communications.
Mismatched Email Domains and Poor Grammar
Always verify the sender’s email address. If a message claims to be from your bank but comes from Gmail.com, it’s likely a phishing attempt. Watch for subtle domain misspellings too.
Poor grammar and spelling errors indicate potential scams. Professional organizations maintain quality control over their content. Multiple mistakes in business emails should raise immediate suspicion.
These simple checks help identify dangerous phishing attempts before they cause harm. Always examine messages carefully when they request sensitive information.
Identifying Suspicious Email and Message Attributes
Technical examination of message components provides critical protection against digital threats. Analyzing specific elements reveals hidden dangers before interaction occurs.
Spotting Suspicious Links and Unexpected Attachments
Hyperlinks represent significant risks in any communication. They can redirect to malicious websites that execute commands without user knowledge.
Always hover your mouse pointer over links without clicking. The pop-up display reveals the true destination address. Compare this URL against the displayed text for mismatches.
Mobile users have different verification methods. Android devices require long-pressing links to view properties. iOS users perform light, long-press actions.
Email attachments pose equal danger. These files often contain malware that activates upon opening. Only download from trusted sources when expecting specific documents.
Understanding Sender Credentials and Email Headers
Modern email clients display authentication warnings when sender verification fails. These banners indicate potential spoofing attempts.
Check for inconsistencies between the sender name and email address. Legitimate organizations maintain consistent credentials across all communications.
Password reset requests should always prompt direct navigation to official websites. Never use embedded links for sensitive account actions.
Strategies for Avoiding Phishing Emails and Fake Support Messages
Your daily digital interactions demand a new level of scrutiny through simple yet effective authentication techniques. Establishing consistent verification habits creates a powerful barrier against fraudulent attempts to access your accounts.
Best Practices for Verifying Sender Authenticity
Legitimate organizations never request sensitive information through unexpected communications. This includes passwords, Social Security Numbers, or credit card details.
When you receive a suspicious message, compare it against known threat databases. Check for inconsistencies in sender names and contact information.
Use independent verification channels like official website numbers. Never trust contact details provided within questionable communications.
Techniques for Hovering Over Links Safely
Always hover your cursor over hyperlinks before clicking. This reveals the true destination address in a pop-up display.
Compare the displayed URL with the link text for mismatches. Legitimate companies use consistent domain names across all platforms.
For urgent account actions, navigate directly to official websites. Use bookmarks or manual typing instead of embedded links.
Effective Steps for Reporting and Mitigating Phishing Attempts
Reporting suspicious activity transforms you from a potential victim into an active participant in cybersecurity. Quick reporting helps protect entire communities by improving detection systems.
How to Report Phishing Emails through Your Email Provider
Microsoft Outlook users can select suspicious messages and use the Report feature. This action removes the threat and helps train security filters.
For Teams communications, hover over questionable content without clicking. Use the More options menu to report security risks properly.
Other email clients require sending messages as attachments to security addresses. This preserves crucial header information for analysis.
Guidelines for Informing IT or Security Administrators
Immediately contact your organization’s IT department if work accounts are compromised. Rapid reporting can prevent network-wide security breaches.
Document all attack details while fresh in your memory. Change passwords on affected accounts and enable multifactor authentication.
Financial information exposure requires immediate bank notification. Serious incidents with financial loss should involve law enforcement.
Using Advanced Tools like ATP and XDR Security
Organizations can implement Advanced Threat Protection for enhanced security. This system uses machine learning to identify novel attacks.
XDR technology provides comprehensive threat detection across multiple platforms. It correlates data to stop sophisticated attacks in progress.
These advanced tools are essential against zero-day threats that bypass traditional filters. They help identify breaches quickly to minimize damage.
Conclusion
Your awareness is the ultimate defense against digital deception. This guide has shown that security depends on both technical checks and psychological insight.
Remember the warning signs: urgent demands, generic greetings, and poor grammar. Always verify sender details before clicking any link. Legitimate companies never request sensitive information through unexpected messages.
Reporting suspicious content helps protect others. Share this knowledge with friends and colleagues. Collective vigilance makes everyone safer.
You now have the tools to identify threats before they cause harm. Stay curious, verify carefully, and trust your instincts. Your new skills make you an informed defender in our connected world.